CVE-2025-55182
Meta React Server Components Remote Code Execution Vulnerability - [Actively Exploited]
Description
A pre-authentication remote code execution vulnerability exists in React Server Components versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0 including the following packages: react-server-dom-parcel, react-server-dom-turbopack, and react-server-dom-webpack. The vulnerable code unsafely deserializes payloads from HTTP requests to Server Function endpoints.
INFO
Published Date :
Dec. 3, 2025, 4:15 p.m.
Last Modified :
Dec. 6, 2025, 2 a.m.
Remotely Exploit :
No
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Meta React Server Components contains a remote code execution vulnerability that could allow unauthenticated remote code execution by exploiting a flaw in how React decodes payloads sent to React Server Function endpoints.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components ; https://nvd.nist.gov/vuln/detail/CVE-2025-55182
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 4fc57720-52fe-4431-a0fb-3d2c8747b827 | ||||
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | MITRE-CVE |
Solution
- Update React Server Components to a secure version.
- Remove vulnerable packages like react-server-dom-parcel.
- Apply security patches for affected packages.
- Validate server function endpoint security.
Public PoC/Exploit Available at Github
CVE-2025-55182 has a 887 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-55182.
| URL | Resource |
|---|---|
| https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components | Patch Vendor Advisory |
| https://www.facebook.com/security/advisories/cve-2025-55182 | Vendor Advisory |
| http://www.openwall.com/lists/oss-security/2025/12/03/4 | Mailing List Patch Third Party Advisory |
| https://news.ycombinator.com/item?id=46136026 | Issue Tracking |
| https://aws.amazon.com/blogs/security/china-nexus-cyber-threat-groups-rapidly-exploit-react2shell-vulnerability-cve-2025-55182/ | Third Party Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-55182 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-55182 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-55182
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
HTML JavaScript
None
None
JavaScript CSS TypeScript HTML
PoC terkait CVE-2025-55182 untuk mendemonstrasikan HTTP-based command execution, dilengkapi multi-scanner logic dan advanced execution helper. Ditujukan untuk pembelajaran teknis, analisis alur eksekusi, serta pengujian terkontrol (VDP, lab, internal testing) dengan izin yang sah.
None
MCP server for Tenable.io vulnerability management integration
Python Shell
React2Shell (CVE-2025-55182)
This is a security exploit tool targeting CVE-2025-55182. It exploits a Remote Code Execution (RCE) vulnerability in React Server Components
Python
React2Shell but for AWS Lambda
Shell Python
None
Dockerfile
None
HTML JavaScript CSS
None
JavaScript HTML CSS Batchfile
None
HTML JavaScript TypeScript CSS
React2Shell Injector
JavaScript HTML CSS Batchfile
None
Dockerfile JavaScript Shell
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-55182 vulnerability anywhere in the article.

-
The Hacker News
ThreatsDay Bulletin: New RCEs, Darknet Busts, Kernel Bugs & 25+ More Stories
This week's updates show how small changes can create real problems. Not loud incidents, but quiet shifts that are easy to miss until they add up. The kind that affects systems people rely on every da ... Read more
-
The Cyber Express
Nation-State Hackers, Cybercriminals Weaponize Patched WinRAR Flaw Despite Six-Month-Old Fix
Russian and Chinese espionage groups continue to exploit an N-day vulnerability (CVE-2025-8088) in WinRAR alongside financially motivated actors, all leveraging a path traversal vulnerability that dro ... Read more
-
The Cyber Express
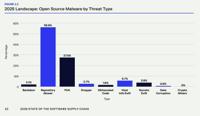
Malicious Open Source Software Packages Neared 500,000 in 2025
Malicious open source software packages have become a critical problem threatening the software supply chain. That’s one of the major takeaways of a new report titled “State of the Software Supply Cha ... Read more

-
The Cyber Express
Hackers Exploit React2Shell Vulnerability to Deploy Miners and Botnets Worldwide
Threat actors have been actively exploiting a critical vulnerability in React Server Components, tracked as CVE-2025-55182 and commonly referred to as React2Shell, to compromise systems across multipl ... Read more

-
CybersecurityNews
Attackers Exploiting React2Shell Vulnerability to Attack IT Sectors
Threat actors have started targeting companies in the insurance, e-commerce, and IT sectors through a critical vulnerability tracked as CVE-2025-55182, commonly known as React2Shell. This flaw exists ... Read more

-
CybersecurityNews
MEDUSA Security Testing Tool With 74 Scanners and 180+ AI Agent Security Rules
MEDUSA, an AI-first Static Application Security Testing (SAST) tool boasting 74 specialized scanners and over 180 AI agent security rules. This open-source CLI scanner targets modern development chall ... Read more
-
Google Cloud
Diverse Threat Actors Exploiting Critical WinRAR Vulnerability CVE-2025-8088
Introduction The Google Threat Intelligence Group (GTIG) has identified widespread, active exploitation of the critical vulnerability CVE-2025-8088 in WinRAR, a popular file archiver tool for Windows, ... Read more
-
Daily CyberSecurity
Incomplete Fix: High-Severity React Server Components DoS Flaw (CVE-2026-23864)
The team behind React, the JavaScript library that powers a vast swath of the modern web, has issued an urgent security advisory warning that previous attempts to patch a Denial of Service (DoS) vulne ... Read more

-
The Cyber Express
New EU Vulnerability Platform GCVE Goes Live, Reducing Reliance on Global Systems
Europe’s long-running conversation about digital autonomy quietly crossed a milestone with the launch of a new public vulnerability platform. The EU Vulnerability Database, created under the GCVE init ... Read more

-
Trend Micro
Introducing ÆSIR: Finding Zero-Day Vulnerabilities at the Speed of AI
Executive summary TrendAI™ has launched ÆSIR, an AI-empowered security research platform that combines advanced automation with human expertise to proactively identify and remediate zero-day vulnerabi ... Read more

-
The Cyber Express
Attackers Targeting LLMs in Widespread Campaign
Threat actors are targeting LLMs in a widespread reconnaissance campaign that could be the first step in cyberattacks on exposed AI models, according to security researchers. The attackers scanned for ... Read more

-
Daily CyberSecurity
Critical React Router Flaws: CVE-2025-61686 Exposes Server Files
Developers relying on the popular React Router library are being urged to patch their applications immediately following the disclosure of multiple high-severity vulnerabilities. The flaws, ranging fr ... Read more

-
hackread.com
CISA Urges Emergency Patching for Actively Exploited HPE OneView Flaw
If your office uses Hewlett Packard Enterprise (HPE) OneView to manage its servers and networking, you need to check your software version immediately. A major security flaw has been discovered that e ... Read more

-
hackread.com
MAESTRO Toolkit Exploiting VMware VM Escape Vulnerabilities
In December 2025, a security team caught a group of hackers just in time. Researchers Anna Pham and Matt Anderson from the firm Huntress recently detailed how these attackers managed to “escape” from ... Read more

-
CybersecurityNews
Hackers Actively Exploiting AI Deployments – 91,000+ Attack Sessions Observed
Security researchers have identified over 91,000 attack sessions targeting AI infrastructure between October 2025 and January 2026, exposing systematic campaigns against large language model deploymen ... Read more

-
hackread.com
n8n Users Urged to Patch CVSS 10.0 Full System Takeover Vulnerability
If your company uses n8n to handle daily tasks, it is time to check your version number. A major security flaw has been found in the platform, and it’s about as serious as it gets. The firm Upwind rec ... Read more

-
CybersecurityNews
Hackers Launched 8.1 Million Attack Sessions to React2Shell Vulnerability
The React2Shell vulnerability (CVE-2025-55182) continues to face a relentless exploitation campaign, with threat actors launching more than 8.1 million attack sessions since its initial disclosure. Ac ... Read more

-
CybersecurityNews
CISA Expands KEV Catalog with 1,484 New Vulnerabilities as Active Exploitation Surges 20% in 2025
The United States Cybersecurity and Infrastructure Security Agency (CISA) has significantly expanded its Known Exploited Vulnerabilities (KEV) Catalog to 1,484 vulnerabilities as of December 2025, mar ... Read more

-
europa.eu
Cyber Brief 26-01 - December 2025
Cyber Brief (December 2025)January 5, 2025 - Version: 1TLP:CLEARExecutive summaryWe analysed 368 open source reports for this Cyber Security Brief[^1].Relating to cyber policy and law enforcement, the ... Read more

-
CybersecurityNews
Threat Actor Exploited Multiple FortiWeb Appliances to Deploy Sliver C2 for Persistent Access
Recent findings indicate that a sophisticated threat actor is actively exploiting multiple outdated FortiWeb appliances to deploy the Sliver Command and Control (C2) framework. This campaign highlight ... Read more
The following table lists the changes that have been made to the
CVE-2025-55182 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Dec. 06, 2025
Action Type Old Value New Value Added Date Added 2025-12-05 Added Due Date 2025-12-26 Added Required Action Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Meta React Server Components Remote Code Execution Vulnerability -
Initial Analysis by [email protected]
Dec. 05, 2025
Action Type Old Value New Value Added CWE CWE-502 Added CPE Configuration OR *cpe:2.3:a:facebook:react:19.0.0:*:*:*:*:*:*:* *cpe:2.3:a:facebook:react:19.1.0:*:*:*:*:*:*:* *cpe:2.3:a:facebook:react:19.1.1:*:*:*:*:*:*:* *cpe:2.3:a:facebook:react:19.2.0:*:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.0.0 up to (excluding) 15.0.5 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.1.0 up to (excluding) 15.1.9 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.2.0 up to (excluding) 15.2.6 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.3.0 up to (excluding) 15.3.6 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.4.0 up to (excluding) 15.4.8 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 15.5.0 up to (excluding) 15.5.7 *cpe:2.3:a:vercel:next.js:15.6.0:-:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary0:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary1:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary10:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary11:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary12:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary13:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary14:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary15:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary16:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary17:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 16.0.0 up to (excluding) 16.0.7 *cpe:2.3:a:vercel:next.js:15.6.0:canary18:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary19:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary2:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary20:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary21:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary22:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary23:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary24:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary25:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary26:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary27:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary28:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary29:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary3:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary30:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary31:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary32:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary33:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary34:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary35:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary36:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary37:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary38:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary39:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary4:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary40:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary41:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary42:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary43:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary44:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary45:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary46:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary47:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary48:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary49:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary5:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary50:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary51:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary52:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary53:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary54:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary55:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary56:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary57:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary6:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary7:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary8:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:15.6.0:canary9:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:16.0.0:-:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary77:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary78:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary79:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary80:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary81:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary82:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary83:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary84:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary85:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary86:*:*:*:node.js:*:* *cpe:2.3:a:vercel:next.js:14.3.0:canary87:*:*:*:node.js:*:* Added Reference Type Facebook, Inc.: https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components Types: Patch, Vendor Advisory Added Reference Type Facebook, Inc.: https://www.facebook.com/security/advisories/cve-2025-55182 Types: Vendor Advisory Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-55182 Types: US Government Resource Added Reference Type CISA-ADP: https://aws.amazon.com/blogs/security/china-nexus-cyber-threat-groups-rapidly-exploit-react2shell-vulnerability-cve-2025-55182/ Types: Third Party Advisory Added Reference Type CVE: https://news.ycombinator.com/item?id=46136026 Types: Issue Tracking Added Reference Type CVE: http://www.openwall.com/lists/oss-security/2025/12/03/4 Types: Mailing List, Patch, Third Party Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Dec. 05, 2025
Action Type Old Value New Value Added Reference https://aws.amazon.com/blogs/security/china-nexus-cyber-threat-groups-rapidly-exploit-react2shell-vulnerability-cve-2025-55182/ Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-55182 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Dec. 04, 2025
Action Type Old Value New Value Removed Reference https://github.com/ejpir/CVE-2025-55182-poc -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Dec. 04, 2025
Action Type Old Value New Value Added Reference https://github.com/ejpir/CVE-2025-55182-poc Added Reference https://news.ycombinator.com/item?id=46136026 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Dec. 03, 2025
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2025/12/03/4 -
New CVE Received by [email protected]
Dec. 03, 2025
Action Type Old Value New Value Added Description A pre-authentication remote code execution vulnerability exists in React Server Components versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0 including the following packages: react-server-dom-parcel, react-server-dom-turbopack, and react-server-dom-webpack. The vulnerable code unsafely deserializes payloads from HTTP requests to Server Function endpoints. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Added Reference https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components Added Reference https://www.facebook.com/security/advisories/cve-2025-55182


