CVE-2026-21509
Microsoft Office Security Feature Bypass Vulnerability - [Actively Exploited]
Description
Reliance on untrusted inputs in a security decision in Microsoft Office allows an unauthorized attacker to bypass a security feature locally.
INFO
Published Date :
Jan. 26, 2026, 6:16 p.m.
Last Modified :
Feb. 11, 2026, 3:40 p.m.
Remotely Exploit :
No
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Microsoft Office contains a security feature bypass vulnerability in which reliance on untrusted inputs in a security decision in Microsoft Office could allow an unauthorized attacker to bypass a security feature locally. Some of the impacted product(s) could be end-of-life (EoL) and/or end-of-service (EoS). Users are advised to discontinue use and/or transition to a supported version.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Unknown
Please adhere to Microsoft’s recommended guidelines to address this vulnerability. Implement all final mitigations provided by the vendor for Office 2021, and apply the interim corresponding mitigations for Office 2016 and Office 2019 until the final patch becomes available. For more information please see: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21509 ; https://nvd.nist.gov/vuln/detail/CVE-2026-21509
Affected Products
The following products are affected by CVE-2026-21509
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | f38d906d-7342-40ea-92c1-6c4a2c6478c8 | ||||
| CVSS 3.1 | HIGH | [email protected] |
Public PoC/Exploit Available at Github
CVE-2026-21509 has a 33 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-21509.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21509 | Vendor Advisory |
| https://www.vicarius.io/vsociety/posts/cve-2026-21509-detection-script-microsoft-office-security-feature-bypass-vulnerability | Third Party Advisory |
| https://www.vicarius.io/vsociety/posts/cve-2026-21509-mitigation-script-microsoft-office-security-feature-bypass-vulnerability | MitigationThird Party Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21509 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-21509 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-21509
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
POC for the Office vulnerability
Python
AI Pentest Proxy es una herramienta profesional de seguridad ofensiva que combina la potencia de múltiples modelos de inteligencia artificial con técnicas avanzadas de pentesting para identificar, confirmar y explotar vulnerabilidades web de forma autónoma.
pentesting pentesting-tools ia-to
Python Shell JavaScript HTML CSS
PowerShell script to check, apply, and test the Kill-Bit protection for the CVE-2026-21509 Microsoft Office zero-day vulnerability affecting Office 2016/2019/LTSC.
apt28 dcom microsoft-office ole-files sysadmin-tool zero-day zeroday cve-2026-21509 powershell-se
PowerShell Python
Advanced Office Macro/DDE injection framework with 2024-2026 bypass techniques (MOTW, AMSI, VBA Stomping, Remote Template Injection, Trusted Location abuse)
Python
CVE-2026-21509 Mitigation
Batchfile PowerShell
None
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
None
YARA rule and python script to detect potential exploits for the CVE-2026-21509 vulnerability in MS Office
YARA Python
Rust library that detects files which look normal but have been crafted to exploit parsing vulnerabilities
exploit mobile
Rust
Overview VortexOracle.efi is a UEFI DXE (Driver Execution Environment) driver built for the EDK2 framework. It implements a hardware-oracle primitive that computes a resonant approximation of π using a specialized mathematical resonance identity at the 33rd layer of a temporal manifold.
C
CVE-2026-21509 is a critical bypass in the Microsoft Office OLE (Object Linking and Embedding) validation engine. While standard "laminar" exploits attempt to manipulate static COM objects, this repository utilizes Theorem 4.2 to achieve a speculative race-condition bypass of the Object Definition Rule (ODR).
Python
Comparative Analysis of AI-Enhanced Hardware Resilience
Microsoft just released emergency patches for CVE-2026-21509, a zero-day in the Office Suite that bypasses OLE/COM mitigations when a user simply opens a file. They think their "Service-side change" for Office 2021+ is a solid wall.
Python
None
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-21509 vulnerability anywhere in the article.

-
The Cyber Express
The State of Cyber Warfare in 2026: Nation-State Attacks, AI Weapons, and the New Digital Battlefield
Cyber operations no longer occur only during wartime. Digital activity now runs continuously alongside diplomacy, sanctions, and military tensions. This has become particularly visible amid escalating ... Read more

-
Daily CyberSecurity
Cyber Escalation: Multi-Vector Attacks Surge Following “Operation Epic Fury”
In the wake of the massive joint offensive launched by the United States and Israel on February 28, the digital battlefield has seen a sharp escalation in activity. A new report from Unit 42 reveals t ... Read more

-
europa.eu
Cyber Brief 26-03 - February 2026
Cyber Brief (February 2026)March 2, 2026 – Version: 1TLP:CLEARExecutive summaryWe analysed 303 open source reports for this Cyber Security Brief1.Relating to cyber policy and law enforcement, the Euro ... Read more

-
The Hacker News
APT28 Tied to CVE-2026-21513 MSHTML 0-Day Exploited Before Feb 2026 Patch Tuesday
A recently disclosed security flaw patched by Microsoft may have been exploited by the Russia-linked state-sponsored threat actor known as APT28, according to new findings from Akamai. The vulnerabili ... Read more

-
The Cyber Express
U.S. Sanctions Russian Broker Over Zero-Day Exploits Theft
The United States has intensified its response to zero-day exploits theft, announcing new sanctions against a Russia-linked cyber tools network accused of stealing sensitive U.S. trade secrets and att ... Read more

-
Daily CyberSecurity
Stealth & Persistence: MuddyWater’s New Rust-Based Payload Mimics Cloudflare and Reddit
While financially motivated cybercrime often dominates the headlines, state-sponsored espionage operates quietly in the background, prioritizing stealth and persistence over quick payouts. A new threa ... Read more

-
Daily CyberSecurity
Hiding in Plain Sight: APT28’s “Operation MacroMaze” Hits European Govs
A new cyberespionage campaign attributed to the notorious Russian state-sponsored group APT28 (also known as Fancy Bear or Forest Blizzard) has been uncovered targeting government entities in Western ... Read more

-
Daily CyberSecurity
Trusted Tool Weaponized: Lotus Blossom Hijacks Notepad++ Updates
A new report from Unit 42 has exposed a highly targeted supply chain attack that turned one of the IT world’s most trusted tools into a weapon. Between June and December 2025, a state-sponsored threat ... Read more
-
Daily CyberSecurity
Inside Job: Abandoned Outlook Add-in “AgreeTo” Steals 4,000 Credentials
The phishing page | Image: Koi Security In a disturbing first for enterprise security, researchers at Koi Security have uncovered a malicious Microsoft Outlook add-in actively harvesting credentials i ... Read more

-
Daily CyberSecurity
Triple Threat Patched: Zimbra 10.1.16 Fixes XSS, XXE & LDAP Injection
Zimbra has rolled out a significant security update for its collaboration suite, releasing Zimbra 10.1.16 to address a spectrum of vulnerabilities ranging from front-end script injection to back-end d ... Read more

-
Daily CyberSecurity
Email Under Siege: Storm-2603 Exploits SmarterMail to Deploy Warlock Ransomware
A new report from ReliaQuest has uncovered a dangerous alliance between a China-based threat actor and a known ransomware strain. The group, identified as Storm-2603, has been caught actively exploiti ... Read more
-
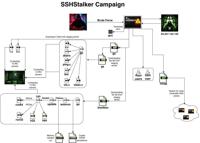
Daily CyberSecurity
Back to the Future: SSHStalker Botnet Revives 2009 Tactics to Hijack Linux Servers
Image: Flare A previously undocumented Linux botnet has been discovered prowling the internet, using a mix of ancient tactics and modern automation to compromise servers. Dubbed SSHStalker by research ... Read more

-
Daily CyberSecurity
CVE-2026-1603: Remote Unauthenticated Attacker Can Steal Ivanti EPM Secrets
Ivanti has rolled out important security updates for its Endpoint Manager (EPM), addressing a pair of vulnerabilities that could expose sensitive credentials to hackers. The release fixes one high-sev ... Read more

-
Daily CyberSecurity
Crash Loop: Palo Alto Networks Flaw (CVE-2026-0229) Forces Maintenance Mode
Palo Alto Networks has issued a security advisory for a denial-of-service (DoS) vulnerability affecting its PAN-OS software, specifically within the Advanced DNS Security (ADNS) feature. The flaw, tra ... Read more

-
Daily CyberSecurity
Apple Zero-Day (CVE-2026-20700) Exploited in the Wild
Apple has issued an emergency security update for its entire mobile ecosystem, racing to close a critical zero-day vulnerability that is currently being used in what the company describes as an “extre ... Read more

-
Daily CyberSecurity
CVE-2026-26007: Python Cryptography Flaw (CVSS 8.2) Leaks Private Keys
A high-severity vulnerability has been discovered in the cryptography Python package, one of the most widely used libraries for securing modern applications. The flaw, tracked as CVE-2026-26007, carri ... Read more

-
Daily CyberSecurity
The Rise of Vibecoding: AI-Generated Malware Exploits React2Shell
A new class of cyberattack has been caught in the wild, one where the code isn’t written by a human hand, but generated entirely by artificial intelligence. Darktrace has released a report detailing a ... Read more
-
Daily CyberSecurity
CVE-2026-25993: Critical EverShop SQL Injection (CVSS 9.3) Exposes Stores
A critical vulnerability has been discovered in EverShop, a modern, developer-focused e-commerce platform built on React and GraphQL. The flaw, tracked as CVE-2026-25993, is a “Second-Order SQL Inject ... Read more

-
Daily CyberSecurity
Excel Trap: New Phishing Campaign Deploys Fileless XWorm RAT
Overview of the XWorm phishing campaign infection chain | Image: Fortinet A new phishing campaign is exploiting an old vulnerability, using malicious Excel files to deploy the potent XWorm Remote Acce ... Read more

-
Help Net Security
Microsoft Patch Tuesday: 6 exploited zero-days fixed in February 2026
Microsoft has plugged 50+ security holes on February 2026 Patch Tuesday, including six zero-day vulnerabilities exploited by attackers in the wild. The “security feature bypass” zero-days Among the ze ... Read more
The following table lists the changes that have been made to the
CVE-2026-21509 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Feb. 11, 2026
Action Type Old Value New Value Added Reference Type CVE: https://www.vicarius.io/vsociety/posts/cve-2026-21509-detection-script-microsoft-office-security-feature-bypass-vulnerability Types: Third Party Advisory Added Reference Type CVE: https://www.vicarius.io/vsociety/posts/cve-2026-21509-mitigation-script-microsoft-office-security-feature-bypass-vulnerability Types: Mitigation, Third Party Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Feb. 10, 2026
Action Type Old Value New Value Added Reference https://www.vicarius.io/vsociety/posts/cve-2026-21509-detection-script-microsoft-office-security-feature-bypass-vulnerability Added Reference https://www.vicarius.io/vsociety/posts/cve-2026-21509-mitigation-script-microsoft-office-security-feature-bypass-vulnerability -
Initial Analysis by [email protected]
Jan. 27, 2026
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:microsoft:office:2016:*:*:*:*:*:x64:* *cpe:2.3:a:microsoft:365_apps:-:*:*:*:enterprise:*:x64:* *cpe:2.3:a:microsoft:365_apps:-:*:*:*:enterprise:*:x86:* *cpe:2.3:a:microsoft:office:2016:*:*:*:*:*:x86:* *cpe:2.3:a:microsoft:office:2019:*:*:*:*:*:x86:* *cpe:2.3:a:microsoft:office:2019:*:*:*:*:*:x64:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2021:*:*:*:*:-:x64:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2021:*:*:*:*:-:x86:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2024:*:*:*:*:-:x64:* *cpe:2.3:a:microsoft:office_long_term_servicing_channel:2024:*:*:*:*:-:x86:* Added Reference Type Microsoft Corporation: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21509 Types: Vendor Advisory Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21509 Types: US Government Resource -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Jan. 27, 2026
Action Type Old Value New Value Added Date Added 2026-01-26 Added Due Date 2026-02-16 Added Required Action Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Microsoft Office Security Feature Bypass Vulnerability -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jan. 26, 2026
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21509 -
New CVE Received by [email protected]
Jan. 26, 2026
Action Type Old Value New Value Added Description Reliance on untrusted inputs in a security decision in Microsoft Office allows an unauthorized attacker to bypass a security feature locally. Added CVSS V3.1 AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H Added CWE CWE-807 Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21509